Configuration Administration and its Numerous Uses
Components
Why does it matter?
In a large company network it is not unusual to have thousands or thousands of community devices. In the event you total all of your switches, routers, firewalls and different network appliances, and then you think about what number of strains of configuration settings apply to each one, you can see you can find a significant investment in your networks' configuration which must be protected.
Identification is the process of figuring out the qualities of a configuration item (any product that might have an end user; this can be a bit of equipment or software, for instance). Improve handle consists of an approval system and protocols required to change the configuration of a configuration item. Status accounting is the capacity to check an object towards the "blueprint" provided by the configuration administration model ensuing from the identification procedure - and lastly, standing accounting is making sure that a vary made in a configuration object has gone based on plan.
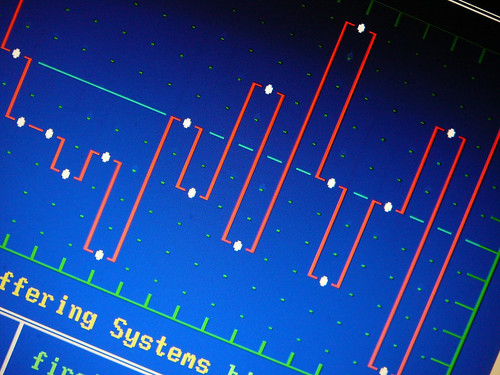
Configuration management by and large bargains with creation, documentation and updating of ordinary settings for all IT components. Change administration and alter detection are also part of the process, which establishes compliance with aims that ensures IT infrastructure reliability. Development of community gadgets and hardware has grown steadily over the years and Server configuration administration has played an important role in creating the performance, security and accounting statistics of the network.
Network Configuration Actions
There are situations that specific action is needed when collecting network configuration of special device upon discovery of any configuration vary or value. The actions should alert the configuration administration team concerning the changes or values that was found either by broadcasting email or lure or by performing special executable command or rectifying specific configuration value. Adding actions to community configuration administration system can easily alert or fix defective configuration equipments ahead of they can cause severe injury to the network.
The design of the SCCB, SCM group, and all the processes, procedures, plans and requirements known as for here tend to be in addition to work needed to determine a source library resource and a librarian which are minimal wants for the typical software project. These groups and documentation will take considerable work to implement and should be specified as part of the project scope if they are to become undertaken.
How does it work?
To date, the increase in network system hardware has applied place at a much faster rate than the equal growth of community administration or network configuration management software. In certain respects it is understandable - Community Devices did not really want managing or configuring originally as they were black containers that either passed data or not. It was simply with the coming of shared network infrastructures like Ethernet the fact that the configuration of addresses and protocols was reformed vital and some consideration made of the community topology to cater for traffic passes and volumes.
Lots more revealed about configuration management here.
Cyrstal Dutta is the Configuration Management expert who also discloses information data recovery renton,compare newegg,cell phone wallpapers on their blog.